Types of Blockchain Technology: What You Need to Know
Blockchain is gaining increased attention as a possible solution to the issues of financial inclusion. A recent report by PricewaterhouseCoopers (PwC) states that over 1.4 billion people worldwide lack access to essential financial services, and the adoption of distributed ledgers may be the key to bridging this gap.
With that in mind, companies and governments are increasingly turning to blockchain so as not to be left on the sidelines of the growing digital economy. However, the industry offers different networks serving different purposes for individuals or businesses, and not all blockchains are created equal.
In this article, we will explore the different kinds of blockchains and their unique characteristics.
Key Takeaways:
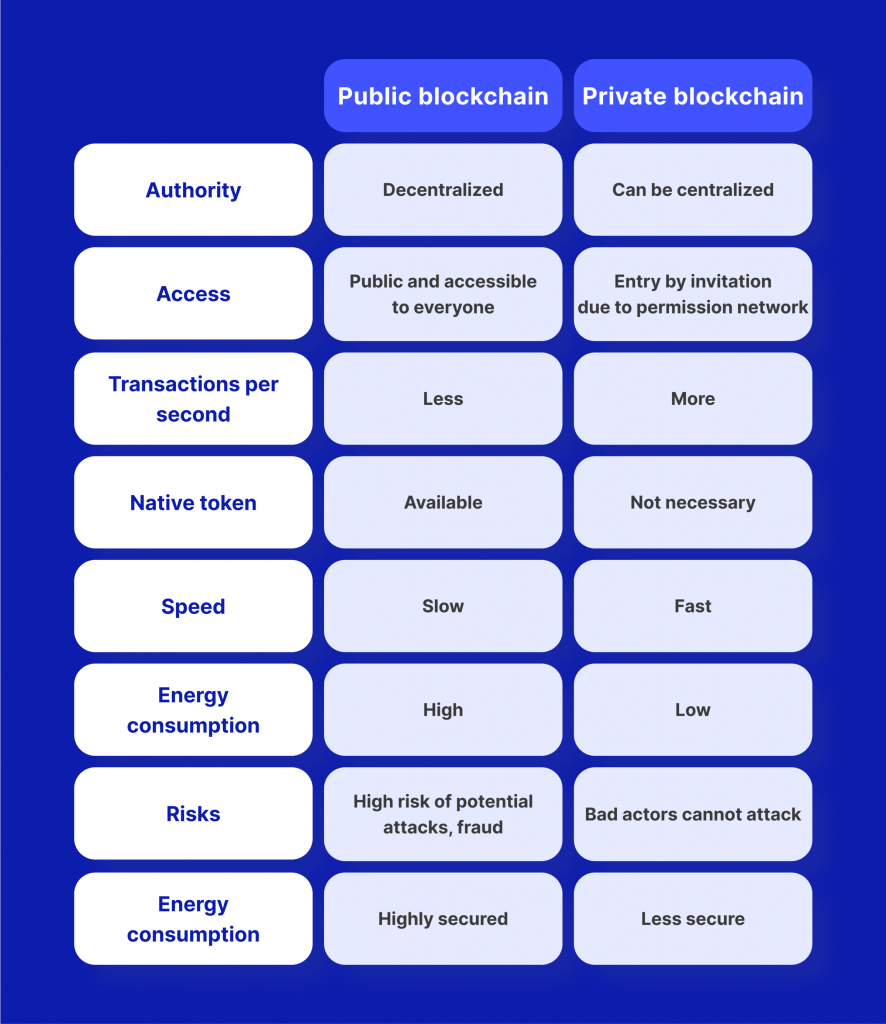
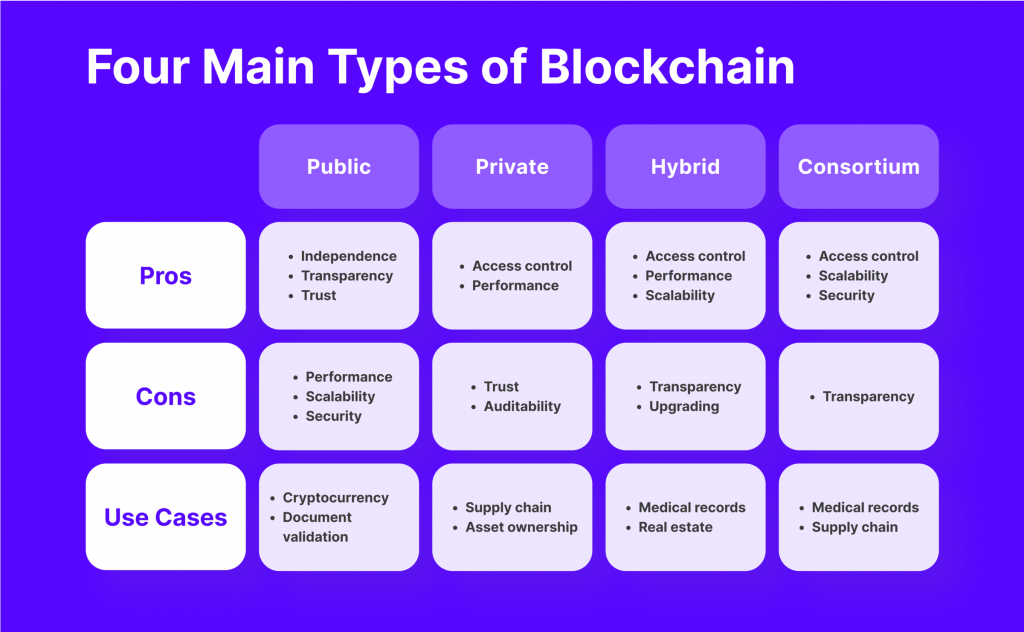
- Public blockchains offer decentralisation and transparency but may have drawbacks such as slow processing times and scalability issues.
- Private chains offer control over data access and usage, making them suitable for industries that require strict privacy measures.
- Consortium chains involve multiple organisations collaborating on a decentralised network.
- Consensus algorithms secure and verify transactions on a blockchain.
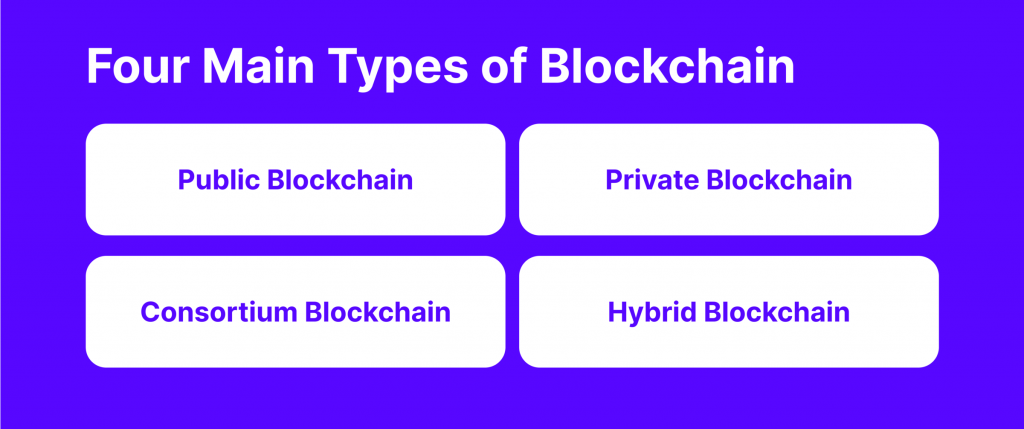
How Are Different Blockchain Networks Classified?
While blockchain may appear to be a technology centred around a specific single concept, there is a great deal of variation between networks. One way to differentiate between them is by their level of decentralisation.
According to this classification, blockchains can be:
- public
- private
- consortium
- hybrid
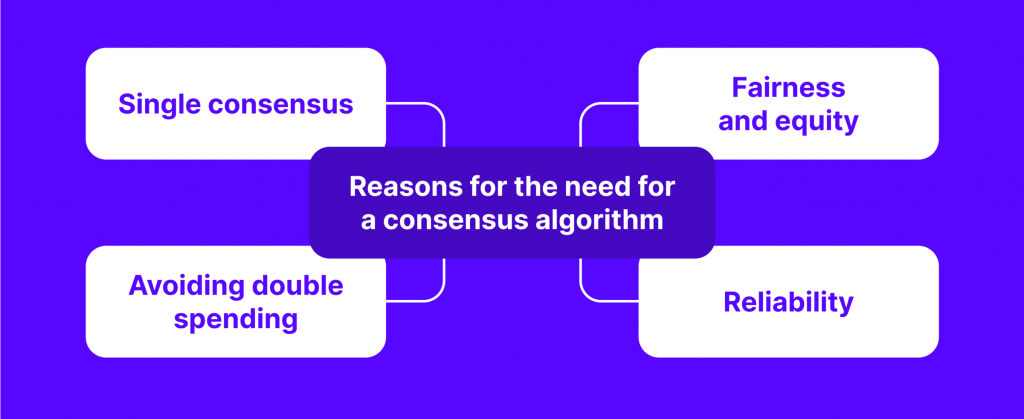
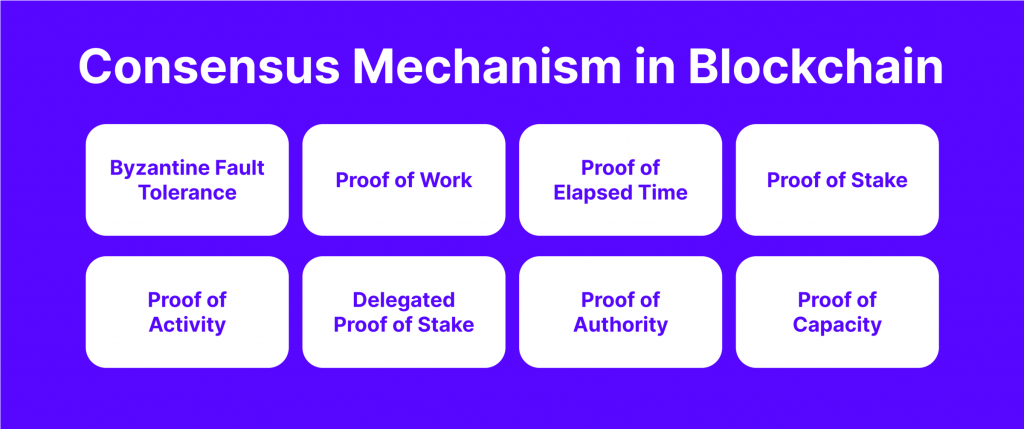
Another way to classify blockchains is by their consensus algorithms. These are the processes through which distributed networks reach an agreement about information on the network. Some common consensus algorithms include:
- Proof of Work (PoW)
- Proof of Stake (PoS)
- Delegated Proof of Stake (DPoS)
- Proof of History (PoH)
- Etc
Public Blockchain
Public blockchains are decentralised networks open to anyone with internet access. They operate on a peer-to-peer network, verifying transactions through a consensus algorithm. Public blockchains’ most widespread consensus methods are PoW and PoS.
How Does It Work?
In a public blockchain network, information is distributed across multiple nodes in the network. The consensus algorithm ensures that these nodes agree on the current state of the ledger.
In the case of PoW, miners solve complicated mathematical puzzles to validate transactions and add them to the blockchain. The first miner to solve the puzzle gets rewarded and broadcasts the new block to the network.
PoS, conversely, selects validators according to how many tokens they own and the length of time they have held them.
Benefits
One of the key advantages of public blockchain networks is their independence from centralised companies. Even if the organisation behind a public blockchain ceases to exist, the network can continue to operate as long as nodes are connected. Public blockchains also offer transparency, as anyone can check transactions on the ledger.
Drawbacks
The network can be slow sometimes, especially as the number of nodes increases. Additionally, these blockchains are not easily scalable. Another potential drawback is the lack of control over access and use, which makes it vulnerable to attacks if a malicious actor gains majority control over the network.
Where Is It Used?
Public blockchains are most commonly used for mining and exchanging cryptocurrencies like BTC, as well as for smart contracts, DeFi and web3 applications, and more. They can also be utilised for creating auditable records, such as electronic notarization of documents and public records of ownership.
Fast Fact
Public blockchains are the most widespread and known type of technology, with tons of projects and tokens launching every day on networks like Solana, Ethereum, Chainlink, Polygon, and others.
Private Blockchain
Private blockchains, also known as managed or permissioned, operate within a closed network and are controlled by a single entity or a group of entities. These blockchains are often used by organisations that prioritise privacy and control over their data.
How Does It Work?
In a private blockchain, permissions are accessible only to a limited number of participants. The controlling entity determines who can view, add, or modify data on it. These blockchains usually operate on a smaller scale compared to public ones and are typically faster and more efficient than their public alternatives.
Benefits
The main advantage of private blockchains is the control it provides over data access and usage. Organisations can set permissions and implement security measures according to their needs. Private blockchains also offer faster transaction processing times and can be more scalable compared to other types.
Drawbacks
Private blockchains are often criticised for their centralised nature, which goes against the core philosophy of decentralisation. The limited number of nodes in a private blockchain network can also make it less secure, as the consensus method can be compromised if a few nodes go rogue. Additionally, the proprietary and closed nature of private blockchains can hinder independent audits and verification.
Where Is It Used?
Private blockchains are ideal for situations in which privacy is crucial, such as trade secret management, auditing, and supply chain management. They are also used in industries that require strict control over data access, such as healthcare and finance.
A good example of a private blockchain in action is Ripple. This business-to-business virtual currency exchange network has gained significant traction among financial institutions for its fast and secure transaction processing.
Fast Fact
The Blockchain Trilemma is a term used to describe the trade-offs between decentralisation, scalability, and security in blockchain. It suggests that any improvement in one area would result in a compromise in another.
Consortium Blockchain
A consortium blockchain involves multiple organisations collaborating on a decentralised network. Unlike private distributed ledgers that are controlled by a single party, consortium blockchains share authority among participating parties.
How Does It Work?
In this type of network, each member organisation has permission to access and participate in the blockchain. However, sensitive information contained within the checked blocks remains hidden from public view.
The consortium blockchain is supervised by one party, known as the supervisor, who oversees the network and prevents any company from having full dominance over it. The supervisor is responsible for setting rules, making changes in balances, and terminating transactions that are deemed faulty by all members.
Benefits
Consortium blockchains offer increased security, scalability, and efficiency compared to public blockchains. With only trusted companies having access, the risk of fraudulent activity is significantly reduced.
Drawbacks
These blockchains are less transparent than public ones, as access and control are limited to the consortium members. The network’s functionality can be impaired if a member node is breached or if the blockchain’s regulations hinder its operation.
Where Is It Used?
The most notable use cases for consortium blockchains are in the financial services industry. Organisations such as R3 have developed popular solutions specifically designed for this sector, allowing for the collaboration of multiple financial institutions.
Another prominent use case is in the shipping industry. Companies like CargoSmart have created non-profit blockchain consortiums aimed at digitising the industry and improving collaboration among maritime operators.
Hybrid Blockchain
Hybrid networks combine the features of both public and private ledgers. These blockchains provide a way to control access to certain data while still allowing for public verification of transactions.
How Does It Work?
In a hybrid blockchain, organisations can set up a private, permission-based system alongside a public permissionless system. This approach helps verify transactions through a smart contract while keeping confidential information private.
Benefits
Hybrid blockchains offer enhanced security, as outside hackers cannot easily mount attacks on the closed ecosystem. They also provide privacy for sensitive information. They are also generally faster and more scalable than public blockchains.
Drawbacks
One of the challenges of hybrid blockchains is maintaining transparency, as certain information can be shielded from public view. Moreover, scaling the blockchain is still a complex task in a hybrid environment. Additionally, there may be a lack of incentive for users to participate or contribute to the network.
Where Is It Used?
These networks are growing in popularity in a wide variety of fields, such as real estate, retail, and highly regulated sectors like financial services, where a high level of privacy for certain information is required while still needing public verification for transactions.
Types of Consensus Mechanisms
Another method of classification of blockchain networks is by consensus methods, which play a crucial role in verifying transactions and securing a blockchain from malicious actors.
Here, we will review the most common and well-known types of consensus algorithms:
Proof of Work
Proof of Work is a mechanism used in many public blockchains, including Bitcoin.
In PoW, miners are competing to solve complicated puzzles, requiring significant computational power. The first miner to solve the puzzle adds a new block to the blockchain and receives a reward.
Proof of Stake
Proof of Stake is an alternative mechanism used in various blockchains, including Ethereum 2.0.
In PoS, validators are chosen according to how many tokens they own and the length of time they have held them. Validators are selected to validate transactions and add them to the blockchain.
PoS is considered more energy-efficient than PoW and offers scalability and reduced centralisation benefits.
Delegated Proof of Stake
Delegated Proof of Stake builds on the PoS model.
In DPoS, token holders vote for delegates who are responsible for validating transactions and maintaining the blockchain. The number of tokens held by a voter determines their voting power. DPoS is known for its scalability and efficiency, making it suitable for high-throughput applications.
Proof of History
Proof of History is a relatively new algorithm introduced by the Solana blockchain.
In PoH, nodes generate cryptographic proofs representing the time passage between events. These proofs are used to order and validate operations on the chain. PoH allows for high-speed transaction processing and has low hardware requirements.
Leased Proof of Stake (LPoS)
Leased Proof of Stake is a variation of PoS that allows users to earn rewards from mining without the need for expensive mining hardware.
LPoS participants lease their tokens to a node operator, who then includes their tokens in the staking pool. The pool operator manages the mining process, and participants receive a share of the rewards based on their leased tokens.
Proof of Importance (PoI)
Proof of Importance used in the NEM blockchain.
It combines the concepts of PoW and PoS, taking into account both the token balance and the transaction activity of each user. PoI rewards users who actively participate in the network and contribute to its growth.
Proof of Burn (PoB)
Proof of burn is an alternative consensus algorithm that addresses the energy consumption issue of PoW systems.
In POB, miners “burn” virtual currency tokens to earn the right to write blocks on the blockchain. The more coins a miner burns, the larger their virtual mining “rig” becomes, increasing their chances of earning rewards.
Fast Fact
The crypto industry knows dozens of consensus algorithms, eight or more of which are widely used in popular networks. However, more and more mechanisms are constantly emerging.
Issues of Blockchain
Despite the wide variety of blockchain options, all systems are faced with a certain level of difficulties that can hinder their effectiveness and widespread adoption. Some of the major challenges include:
Scalability Issues
Scalability has been a major concern for the technology, particularly public blockchains. As a greater number of transactions are added to the system, the network becomes slower and less efficient.
Various solutions, such as sharding and layer-two protocols, are being developed to improve scalability without sacrificing security and decentralisation. These solutions aim to increase transaction throughput and reduce congestion on the blockchain network.
Interoperability
Interoperability is another area of focus for developers. As there are many kinds of blockchains, each with its own unique features and protocols, it is difficult for them to communicate with one another and share data.
Today, interoperability protocols and frameworks are being developed to enable seamless integration and communication between platforms.
Privacy
Privacy remains a concern for certain applications. Privacy-enhancing technologies, such as zero-knowledge proofs (ZKPs) and secure multi-party computation, are being explored to provide privacy features without compromising the security and integrity of systems.
Bottom Line
There are different types of blockchains, each serving their roles. Understanding each blockchain’s role and functionality is important to succeed in the business and adjust it to the latest technology trends.
FAQs
What are the layers of blockchain technology?
Blockchain operates through six interconnected layers: hardware infrastructure, data, network, consensus, and application. Each layer has a specific role in ensuring networks’ secure and transparent functioning.
What are the main principles of blockchain?
Some of the main principles of distributed ledger technology include decentralisation, immutability, and transparency.
What is the best consensus algorithm?
There is no “best” algorithm, as every algorithm has strengths and weaknesses. For example, PoW is known for its security but requires a large amount of processing power, while PoS has lower energy costs but can potentially lead to centralisation. It ultimately depends on the specific needs and goals of a user, project or system.